We can help your IPTV Provider (or Portal admin) to get the settings right (on best effort basis) however making those changes is entirely up to the Provider.
A capable system administrator can easily perform all the steps below however not all Portal admins have the needed (root) access (to the Portal servers). Also Portal resellers have limited access.
We have no access or control over any Portals or streams and we do not provide any streaming services!
—
We recommend your users to use SmartSTB+ if it’s available on their platform, however due to OS and hardware limitations this app is not available on all platforms.
The SmartSTB+ (plus) app and Smart STB app on Apple’s iOS/tvOS and RokuTV devices connects directly to the Portal or Playlist. Some devices with OS limitations may use our app servers for gathering EPG info and TV logos. Usually there is no need to adjust the portal settings however in some cases some portals may not be fully compatible. You can also use m3u playlist with support for TV logos, EPG and categories for the TV channels.
As of now SmartSTB+ is available on devices in all regions running Android 9 or newer including Android TV and Google TV, FireTV and Firestick. A global Roku TV version is coming very soon.
—
Cloudflare users – please check the end of the article for specific instructions
—
Dear Service Providers,
In order to guarantee smooth service and avoid compatibility problems we recommend you white list (or unlock in case of blocked) our Server IP’s in your Panels, Streaming Servers and Billing Servers.
The application works by connecting to your portal thru our app servers (except for Smart STB+ and Smart STB on iOS and tvOS devices made by Apple and RokuTV which they all connect directly).
The app users may appear connecting to the Portal from our app servers’s IP (depending on region and availability, see the IP’s below)
We pass smart TV’s public IP via X-Forwarded-For header, please see below!
Devices running Smart STB always access any streaming links directly (from the TV’s Public IP address, we never proxy any streaming traffic!).
Please make sure your Portal detects the Public IP address of each TV by reading “X-Forwarded-For” headers coming from our app users.
This way you will always have the Smart TV’s public IP address and make the app compatible with your Portal.
Some popular middleware solutions are doing this automatically.
Doing this is strongly recommended, it will fix possible black screen problems with your portals too.
Please do not forget to do this on all your Portal servers, streaming servers, time shift servers, recording (npvr), archive and catchup servers, billing servers and everything associated with your service.
Otherwise, for example, if you don’t do it on your Time shift/recording servers, then Time shift may not work for the Smart STB users.
Other example case: app may not remember the username and password if it’s blocked on the authentication server but not blocked on the Portal.
Properly unblocking the app for your IPTV service will fix the “Portal may be having problems” message.
Our current list of app IP’s is :
Australia (au.smart-stb.tv) | 139.99.195.10 |
Brazil 2, South America (br2.smart-stb.tv) | 108.181.68.167 |
Balkans (UAT) (bg2.smart-stb.tv) | 82.118.227.12 |
Bulgaria (bg1.smart-stb.tv) | 185.141.63.105 |
Bulgaria (bg3.smart-stb.tv) | 82.118.234.58 |
France – Bourgeoisie (fr.smart-stb.tv) | 51.38.52.15 |
India (in.smart-stb.tv) | 206.189.131.214 |
Italy (it4.smart-stb.tv) | 95.141.36.107 |
Luxembourg + Russia (lux.smart-stb.tv) | 198.251.84.231 |
Rest of the world + Asia (Wide) (world1.smart-stb.tv) | 46.101.135.71 |
Romania (ro.smart-stb.tv) | 45.15.23.22 |
Singapore + Oceania (sg.smart-stb.tv) | 139.99.43.35 |
South Africa + Lesotho (sa3.smart-stb.tv) | 102.69.156.30 |
Spain + Portugal HA (sp5.smart-stb.tv) | 89.38.226.90 |
UK + Ireland (uk.smart-stb.tv) | 51.38.80.221 |
UK3 + Ireland (uk3.smart-stb.tv) | 206.189.21.107 |
Ukraine (ua1.smart-stb.tv) | 82.118.17.203 |
USA (West) + North Continental Americas (us4.smart-stb.tv) | 205.185.126.190 |
USA (East 2) (us5.smart-stb.tv) | 37.120.216.206 |
USA (East) and Canada (us6.smart-stb.tv) | 138.197.124.132 |
World Web and Portal Validator #1 (www.smart-stb.net) | 167.235.221.26 |
EDGE (edge.smart-stb.tv) | 82.118.227.12 |
UAT (uat.smart-stb.tv) | 82.118.227.12 |
Click here for an NGINX sample config containing all of the IP’s above.
IP’s listed above are for international app delivery and can change. There are possible regional or local servers in certain areas that may not be listed here. Read below for them.
In case of local network delivery: Local IP’s like 10.20.30.40 are used in cases where IPTV and app delivery is done in a Local Area Network inside your local ISP. Local VLAN ID for Smart STB is 155 or whatever is used for IPTV delivery unless stated otherwise in your corporate activation email.
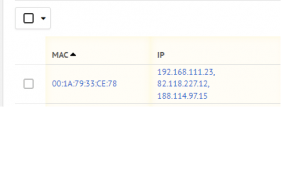
One good way to tell what server IP is used by the client is to ask them to press any number key on the Remote during “Loading Portal” – they will get similar screen:

In this example [edge.smart-stb.tv] is the local server’s name and [10.20.30.40] the IP address.
In case you use Apache2 configuration, you do not need to do anything special, default configuration should give you the correct Client IP’s
<VirtualHost *:88>
ServerAdmin webmaster@localhost
DocumentRoot /var/www
<Directory /var/www/stalker_portal/>
Options -Indexes -MultiViews
AllowOverride ALL
Require all granted
</Directory>
ErrorLog ${APACHE_LOG_DIR}/error.log
CustomLog ${APACHE_LOG_DIR}/access.log combined
</VirtualHost>
In case you use nginx or other similar solution, we advise you to add those options to your nginx configuration for your Portals, Streaming Servers and Billing Servers to guarantee app compatibility and correct client IP’s visible to you at all times.
server {
listen 80;
server_name localhost;
location / {
proxy_pass http://127.0.0.1:88/;
proxy_set_header Host $host:$server_port;
proxy_set_header X-Real-IP $remote_addr;
###proxy smart stb
set_real_ip_from 209.141.39.88;
set_real_ip_from 198.251.83.217;
set_real_ip_from 82.118.17.203;
…
}
location ~* .(htm|html|jpeg|jpg|gif|png|css|js)$ {
root /var/www;
expires 30d;
}
}
One good way to check if the client’s IP you see is correct is to login to your Panel and see the user’s info. If the IP is like our app server IP’s then the configuration is wrong. If the IP address you see is the same as the public IP address of your client, then everything is okay.

In this example clients with Virtual MAC 00:1A:79:95:9E:95 and 00:1A:79:01:02:03 have WRONG login and their actual Public IP is not visible.
This can cause black screen problems for the example clients.
Individual guides for other most popular middleware platforms is coming soon, examples above are for Ministra.
Cloudflare
Cloudflare users – please perform this instruction specific to Cloudflare to allow our app to function correctly for portals behind Cloudflare servers.
If you want to use Cloudflare you must put their server IP ranges and get CF-Connecting-IP for your regular MAG box users and use X-Forwarded-For for your Smart STB users.
Here is an example working configuration we tested, please note CloudFlare IP’s may change:
(put in nginx before location /)
server_name your-domain-name.tld;
set_real_ip_from 173.245.48.0/20;
set_real_ip_from 103.21.244.0/22;
set_real_ip_from 103.22.200.0/22;
set_real_ip_from 103.31.4.0/22;
set_real_ip_from 141.101.64.0/18;
set_real_ip_from 108.162.192.0/18;
set_real_ip_from 190.93.240.0/20;
set_real_ip_from 188.114.96.0/20;
set_real_ip_from 197.234.240.0/22;
set_real_ip_from 198.41.128.0/17;
set_real_ip_from 162.158.0.0/15;
set_real_ip_from 104.16.0.0/13;
set_real_ip_from 104.24.0.0/14;
set_real_ip_from 172.64.0.0/13;
set_real_ip_from 131.0.72.0/22;
In case you want to proxy to Apache2 (assuming apache2 port is 88) thru nginx please configure reverse proxy like this:
location / {
proxy_pass http://127.0.0.1:88/;
proxy_set_header Host $host;
proxy_set_header X-Real-IP $proxy_add_x_forwarded_for;
proxy_set_header CF-Connecting-IP $http_CF_Connecting_IP;
real_ip_header X-Forwarded-For;
…
}
In case you use Apache2 you will need to enable remoteip module (usually done by sudo a2enmod remoteip command on popular distros)
Please note that first IP is IP of the Smart TV, second IP is our app DP server and third IP is usually Cloudflare server which processed all this.
More in-dept information available here:
https://support.cloudflare.com/hc/en-us/articles/200170786-Restoring-original-visitor-IPs
And technical info is available here: